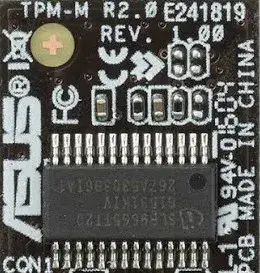
Unlike many Linux users, I really liked the idea of the TPM. So long as I fully control the keys, integration with a security chip to authenticate my system would be a nice bonus and represents a natural extension to secure boot. We already take this approach in principle with smartphones.
On the other hand, it’s becoming a lot harder to actually own your devices and run code of your own choosing on smartphones. It’s a tool that so far has generally been used to serve the interests of the vendor over the user.
It would be a fine system if the keys were stored on the encrypted volume that the TPM decrypts
That probably makes sense. Most people don’t have the risk of a malicious actor sniffing their TPM bus and those that do can opt in. Everybody else can still benefit from a TPM
The intent was on better TPM security after a prior security demonstration showed TPM key recovery from Microsoft Windows BitLocker as well as TPM sniffing attacks.
I am not sure if this is a good change. Isn’t this “dangerous”?
The hope is that now it’s disabled by default, the Linux kernel developers can spend more time evaluating the security benefits and performance optimizations to make it worthwhile to re-enabled by default in a future Linux kernel version.
I’m confused. They disable security feature and then want spend time on the benefits and performance optimizations, to possible enable it again?
The TPM 2.0 implementation (mandated by Microsoft) is flawed. That much is certain.
If you’d like to know more details about the “benefits” and vulnerabilities of the standard, feel free to read the relevant wikipedia article: https://en.wikipedia.org/wiki/Trusted_Platform_Module
In my personal opinion, the TPM as a whole seems like a “solution in search of a problem”, and developments that were able to foil its protection as early as 2010 from state and non-state actors should be a massive red flag.
Physical security is very hard
TPM is a useful to help ensure physical security. TPM isn’t perfect but it is decent for what it is.
That assumes you can trust the unauditable. I can only accept open hardware, with verification of random samples.
If you use TPM for signing, that is not an issue most of the time. But if you store decryption keys for a storage device there that’s not a good idea.
Where would you store it then?
Preferably in your brain and maybe partially in a smart card protected by a pin?
Yes, currently I’m using my brain for that and was thinking a security key such as Yubikey with touch requirement + PIN. But at least on Linux there is no support for that, or is it?
Edit: Ha, there actually is - https://mhdez.com/posts/unlocking-encrypted-linux-with-a-yubikey/
AFAIK there is. But even if not, it simulates a keyboard which can input your passphrase. Also modification of the initrd is a matter of providing a bash script or binary to launch which returns the passphrase in the crypttab file and adding it to the correct directory.
From what I read so far, hardware key is just another way to decrypting, not the required. So it’s just a convenient method to avoid typing a (long) password and instead just few PIN chars. So, if somebody gets hold of password, can still decrypt the disk even without the hardware key. Not perfect, but still better than only password.
another encrypted medium
@cm0002 Never understood why one should use tpm when there are good old passwords. It would be better to enforce a long password. To me TPM always looked like a marketing strategy masked by security tools: in the end it’s a device that makes it mandatory to use your hard-drive on a specific machine. It’s even weaker than a good password. Am I wrong?
TPMs protect against evil maid attacks
Android has a nice solution with the system vs user encryption
@possiblylinux127 And allows to decrypt the disk if someone steals your laptop: it can just turn it on to read it…
That isn’t how TPMs work
The TPM checks the signature of the software with the signature it has internally. If that signature changes it will refuse to release the keys.
@possiblylinux127 Exactly. So if someone steals your laptop it can just press the power on button to read your disk. Security my ass.
…if they can log in
- Password is not mandatory
- Some organizations require ultra-simple password formats (e.g. 6 digits)
- Afaik password is not enabled by default in windows
Call this security… It’s just a marketing lock-in strategy. A good old password is all you need for encrypting a disk.
…Except none of that is true